Beyond Signatures: How Machine Learning and Autonomous Agents Are Reshaping Intrusion Detection
Introduction
For decades, intrusion detection systems (IDS) have relied on a simple yet effective approach: comparing network traffic against a database of known attack signatures. While this method catches many threats, it struggles with novel attacks, encrypted traffic, and the subtle patterns of advanced persistent threats. Today, a new wave of technology is transforming the landscape. By combining machine learning with autonomous agents, modern IDS are moving from static pattern matching to dynamic, context-aware analysis. This article explores the evolution through examples like SnortML and the emerging role of agentic AI.
The Limitations of Signature-Based Detection
Traditional signature-based IDS, such as standard Snort, work by comparing incoming data against a library of predefined patterns—like a fingerprint matching game. When a packet matches a known malicious signature, an alert is generated. However, this method has several critical weaknesses:
- Zero-day attacks — Novel threats have no signature, so they go undetected until a signature is created.
- Evasion techniques — Attackers can obfuscate payloads or fragment packets to avoid matching.
- High false positive rates — Legitimate traffic that resembles an attack triggers unnecessary alerts.
- Lack of context — A signature doesn't consider the bigger picture, such as normal baseline behavior or accompanying events.
These limitations have driven the search for more intelligent detection methods that can understand intent and context rather than just exact matches.
Enter Machine Learning: SnortML and Contextual Analysis
Machine learning (ML) introduced a paradigm shift. Instead of asking, "Does this match a known pattern?" the system now asks, "Does this make sense in context?" SnortML is a prime example of this evolution. It extends the open-source Snort IDS by incorporating ML models that analyze network traffic for anomalies based on learned behaviors.
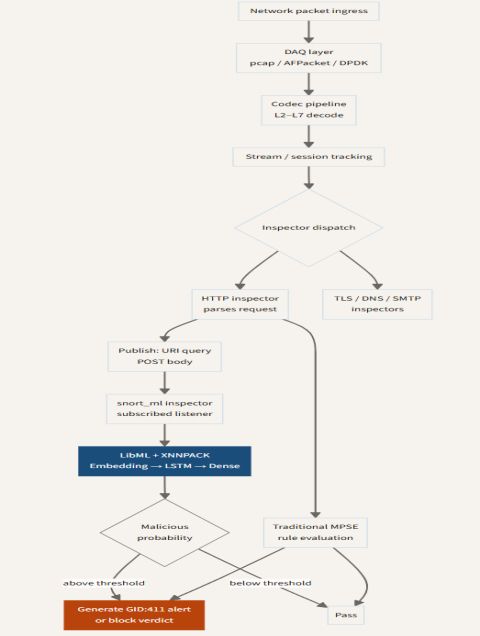
How SnortML Works
SnortML uses supervised learning on labeled datasets to train models that recognize malicious versus benign traffic. But its real power lies in its ability to generalize. After training, the model can identify variants of known attacks and even flag suspicious activities that don't match any existing signature. This is achieved through feature extraction: examining packet payloads, timing, protocol anomalies, and more. The output is a confidence score, which can be used alongside traditional rules to reduce false positives.
From Pattern Matching to Anomaly Detection
The transition from signature-based to ML-based detection is not just about adding another layer—it's about changing the fundamental question. A signature check is binary: match or no match. ML introduces probabilistic reasoning. For example, a slight deviation in the header of a DNS request might be flagged as suspicious even if it doesn't match any known exploit. This contextual awareness allows the IDS to catch the “unexpected” — such as a DNS tunnel using a custom encoding.
The Rise of Agentic AI in Cybersecurity
Machine learning alone, however, still requires human oversight. The next frontier is agentic AI — autonomous systems that not only detect threats but also take action. These agents operate with a degree of self-direction, adapting to changing environments and making decisions in real time.
Autonomous Decision-Making
An agentic IDS builds on ML by adding a decision-making layer. Instead of just raising an alert, an autonomous agent can correlate multiple signals, evaluate risk, and initiate a response—such as blocking an IP, isolating a host, or adjusting firewall rules. This shifts the paradigm from “detect and report” to “detect, analyze, and act.” For example, if an agent sees a sudden burst of traffic to a rare port combined with failed authentication attempts, it might preemptively block the source while still logging the event for review.
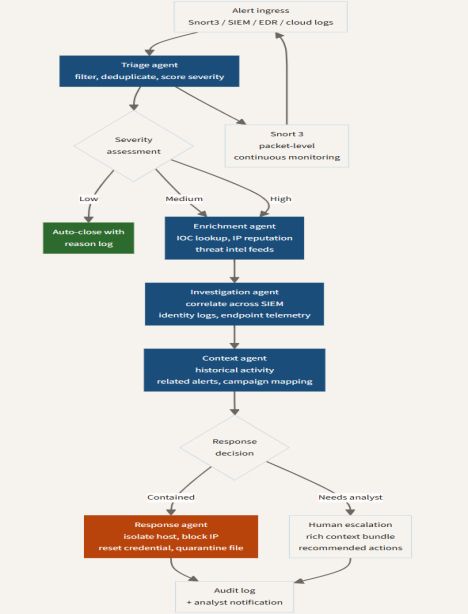
Real-Time Contextual Responses
Agentic AI thrives on context. It maintains a model of the network's normal state and continuously updates it. When an anomaly is detected, the agent considers not only the current packet but also recent events, time of day, user roles, and historical patterns. This reduces false positives and enables nuanced responses. For instance, a spike in outbound data to a known cloud provider might be considered low risk for a developer, but high risk if it comes from a server that never makes external connections.
The Evolving Architecture of Intrusion Detection
The integration of ML and agentic AI is not just adding features; it's fundamentally changing the architecture of IDS. Modern systems are becoming more modular, distributed, and self-adapting.
Hybrid Approaches
Many organizations adopt a hybrid model: signature rules for known threats, ML for anomalies, and agentic AI for automated response. This layered defense ensures that even if one method fails, others provide coverage. For example, SnortML can be configured to run alongside traditional Snort rules, with a weighting mechanism that fuses both signals. Agentic AI can then oversee the combined output and orchestrate actions across multiple security tools.
Future Directions
Looking ahead, we can expect even deeper integration with threat intelligence feeds, more advanced unsupervised learning for zero-day detection, and multi-agent systems that collaborate across network segments. The ultimate goal is a self-healing security infrastructure that can adapt to attacks in real time without human intervention. As introduced earlier, this evolution is shifting the core question from "Does it match?" to "Does it make sense?" — a change that will define the next generation of cybersecurity.
Conclusion
The journey from simple signature matching to intelligent, agent-driven detection represents a quantum leap in how we approach network security. Tools like SnortML demonstrate the power of context-aware machine learning, while agentic AI promises autonomous, adaptive defense. By embracing these technologies, organizations can stay ahead of increasingly sophisticated threats. The sensor is no longer just watching; it's thinking — and acting.
Related Articles
- The Prepersonalization Workshop: A Blueprint for Successful Data-Driven Design
- 7 Game-Changing Insights from the Humanoid Robot That Won a Marathon Using Smartphone Tech
- From Cleaning Floors to Mobile Screens: Dreame's Surprising Smartphone Announcement
- 10 Essential Insights for Validating Non-Deterministic Agent Behavior in CI/CD
- Europe's Blueprint for a Civilian DARPA: A Step-by-Step Guide to Countering Drone Threats
- 8 Critical Insights Into the Real-World Demands of Bionic Technology
- Finding the Right Balance: How to Identify Transparency Moments in Autonomous AI Agents
- NVIDIA and ServiceNow Unleash Project Arc: Autonomous Desktop Agents for Enterprise