Quick Facts
- Category: Cybersecurity
- Published: 2026-05-03 09:13:13
- Securing Your cPanel Server Against Critical Authentication Flaws: A Step-by-Step Update Guide
- AI’s Hidden Cost: The ‘Bug-Free’ Workplace That’s Eroding Team Bonds, Experts Warn
- Microsoft Drops 34-Fix Windows 11 Update with New Xbox Mode, Startup Boost
- 5 Reasons Why Xiaomi's Variable Aperture Proves Samsung and Google Are Falling Behind
- 10 Essential IT Fundamentals You Must Know: From Hardware to Docker
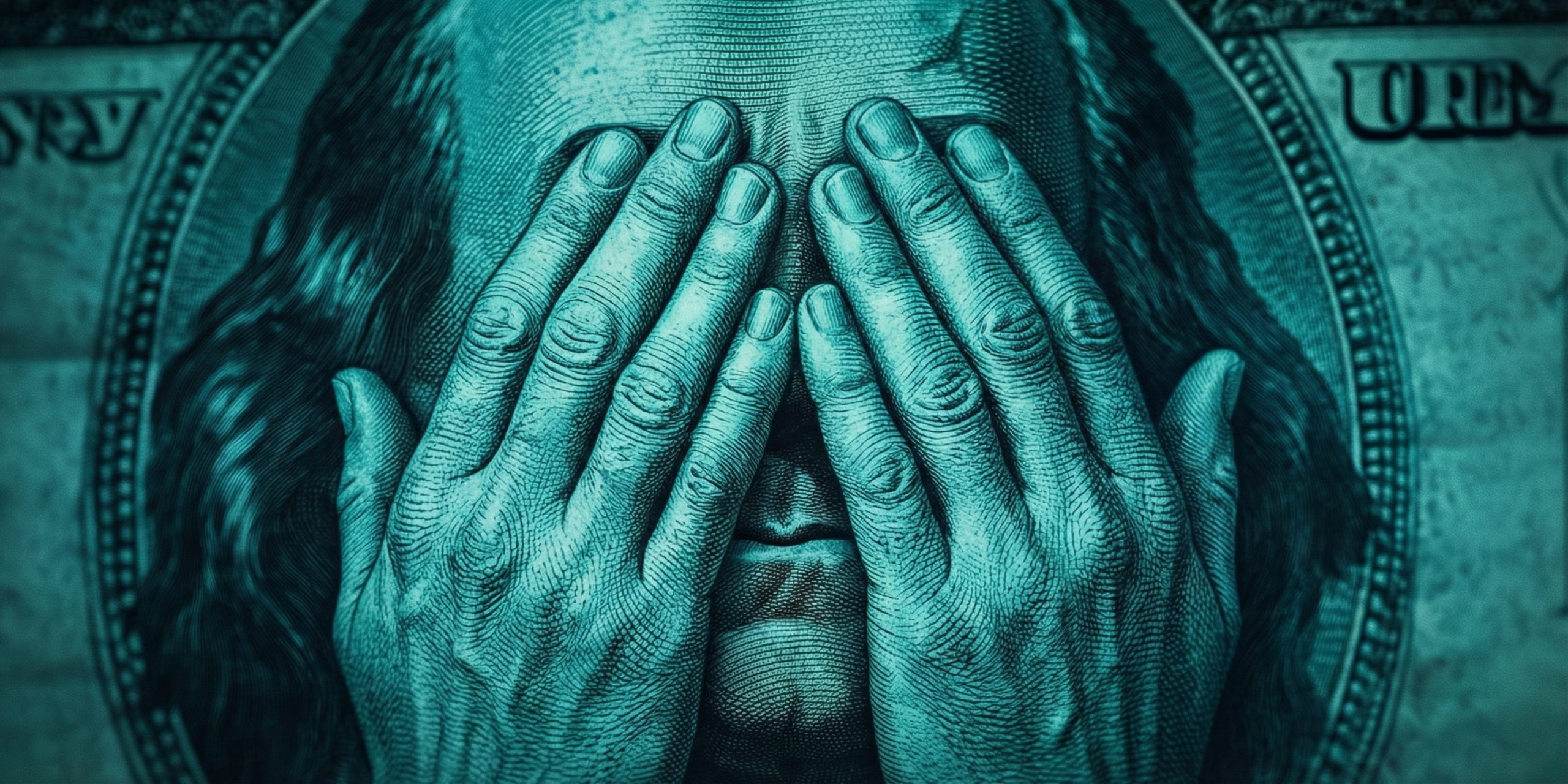
As we move through 2025, the financial cyberthreat landscape is undergoing a significant transformation. Traditional PC banking malware is declining, but attackers are shifting tactics toward credential theft via infostealers and more targeted phishing campaigns. Mobile banking malware continues to rise, and the dark web economy is booming with stolen data. This Q&A explores the major findings from Kaspersky's analysis for 2025—based on anonymized data from its security network, public sources, and dark web monitoring—and offers an outlook for 2026. Click on any question below to jump directly to its answer.
- How is the financial threat landscape changing in 2025?
- What are the top phishing categories in 2025?
- Why is PC banking malware declining while mobile malware grows?
- How do infostealers fuel the dark web economy?
- What regional differences appear in phishing campaigns?
- What should we expect for financial cyberthreats in 2026?
How is the financial threat landscape changing in 2025?
In 2025, financial cyberthreats are evolving away from traditional malware toward credential theft and social engineering. While PC-based banking Trojans have declined in relative prevalence, attackers now rely more on infostealers—malware designed to harvest login credentials, payment data, and system information. These stolen credentials are then aggregated and reused across multiple platforms, often sold on the dark web. This shift means that instead of developing complex new malware, cybercriminals focus on exploiting already stolen data through automation and targeted phishing. The result is a more scalable threat that affects both individuals and financial institutions, with fraud operations becoming more destructive.
What are the top phishing categories in 2025?
Phishing campaigns in 2025 show a clear pivot toward digital services and e-commerce. According to Kaspersky’s data, the most mimicked categories on phishing and scam pages are:
- Web services (16.15%) – including email, cloud storage, and productivity tools.
- Online games (14.58%) – growing rapidly as attackers target impulsive users.
- Online stores (14.17%) – taking advantage of shopping habits.
Compared to 2024, traditional banking lures are less dominant. Instead, cybercriminals are adapting to regional user behavior and creating context-aware lures. Instant messaging apps and global internet portals remain significant targets because they act as communication hubs. This maturation of phishing operations means attacks are fewer in volume but more convincing and targeted.
Why is PC banking malware declining while mobile malware grows?
The decline in PC banking malware doesn’t mean the threat is gone—it’s simply shifting. Established malware families still operate, but attackers increasingly prioritize credential access over deploying complex Trojans. Meanwhile, mobile banking malware continues its upward trajectory. As smartphone usage for banking and payments surges, cybercriminals develop mobile-specific Trojans that intercept SMS-based two-factor authentication, overlay legitimate banking apps, and steal credentials directly on the device. This divergence is detailed in Kaspersky’s separate mobile malware report. Essentially, attackers follow the money: where users transact (mobile), that’s where malware evolves. The PC channel is now secondary for direct financial theft.

How do infostealers fuel the dark web economy?
Infostealers have become the engine of financial cybercrime in 2025. These malware strains—like RedLine, Vidar, and Raccoon—collect a treasure trove of data from infected devices: saved passwords, cookies, credit card numbers, crypto wallets, and even full identity profiles. This stolen data is then traded on dark web marketplaces at scale. Cybercriminals can purchase a batch of credentials for a few dollars or subscribe to services that constantly update with fresh data. The availability of such information enables widespread fraud, from account takeovers to synthetic identity creation. Since infostealers are often spread via phishing links or fake downloads, the barrier to entry for criminals is low, making this a persistent and growing threat for financial systems.
What regional differences appear in phishing campaigns?
Regional patterns in 2025 phishing campaigns reveal how attackers adapt their lures to local contexts. For instance, in regions with high e-commerce penetration, phishing pages mimic popular online stores, while in areas where online gaming is booming, gaming credential theft rises. Instant messaging apps are heavily targeted in countries where they dominate communication, such as WhatsApp in Latin America or WeChat in Asia. Kaspersky’s analysis indicates that attackers tailor social engineering to cultural norms and popular services, making the scams harder to detect. This localized approach contrasts with the broad, generic campaigns of previous years. Even categories like global internet portals show regional variation in which specific services are impersonated. The bottom line: phishing is no longer one-size-fits-all—it’s contextually aware.
What should we expect for financial cyberthreats in 2026?
Looking ahead to 2026, we can expect several trends to intensify. First, infostealers will likely become even more sophisticated, possibly using AI to automate tailored attacks. Second, mobile banking malware will continue to grow as smartphones become the primary banking tool for many. Third, the dark web economy will expand, with full identity kits (including biometric data) traded more frequently. Fourth, phishing will become hyper-personalized, leveraging data from breaches to craft convincing lures. Finally, we may see a rise in API-based fraud targeting financial service interfaces directly. Defenders will need to invest in behavioral analytics, strong authentication, and continuous dark web monitoring to keep pace. The shift from malware-centric to credential-centric crime means that securing user identity becomes the top priority.